Your AI SOC Analyst Team
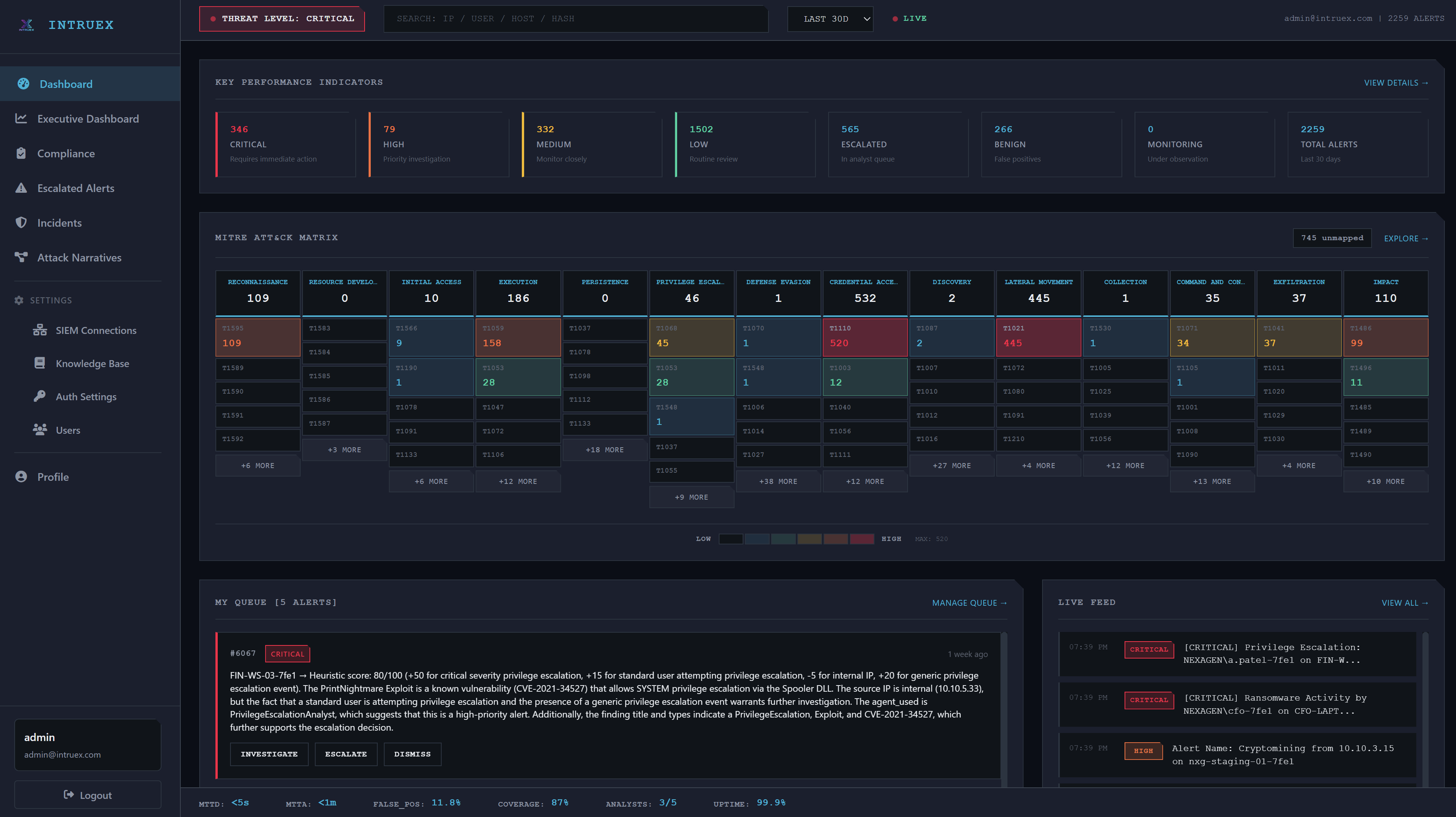
Specialist AI agents triage, enrich, and disposition every alert from your SIEM — so your analysts focus on real threats.
Patent pending
Designed to reduce SOC workload by automating triage, enrichment, and disposition for every alert — freeing analysts to focus on confirmed threats.