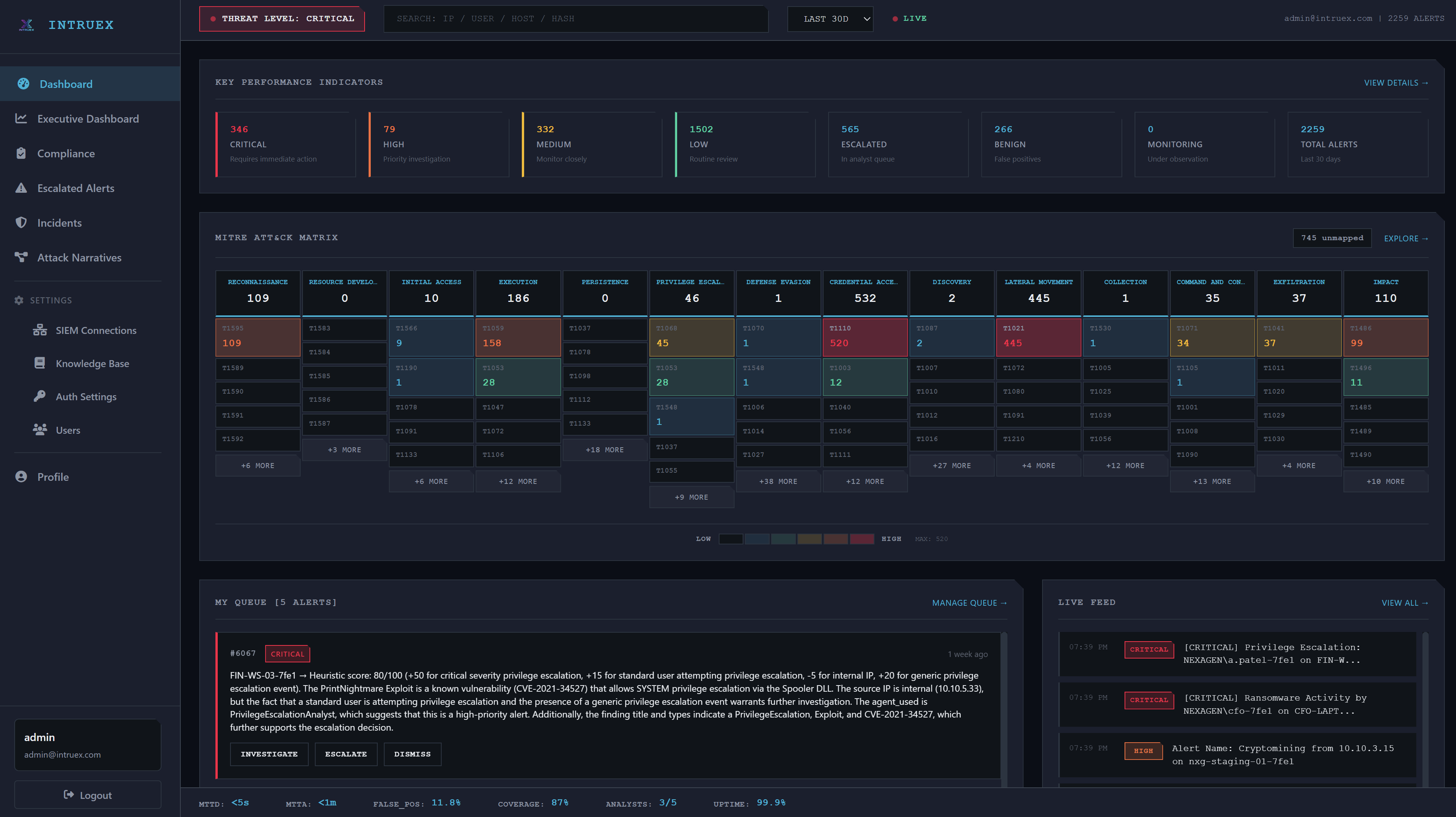
Attack Narratives & Campaign Detection
Intruex doesn't just triage alerts — it connects the dots. Related alerts are automatically correlated into attack campaigns with plain-English narratives that tell the full story.
Automatic Alert Correlation
Related alerts are automatically grouped into attack campaigns based on shared indicators — IPs, users, hosts, and timing patterns. No manual correlation required.
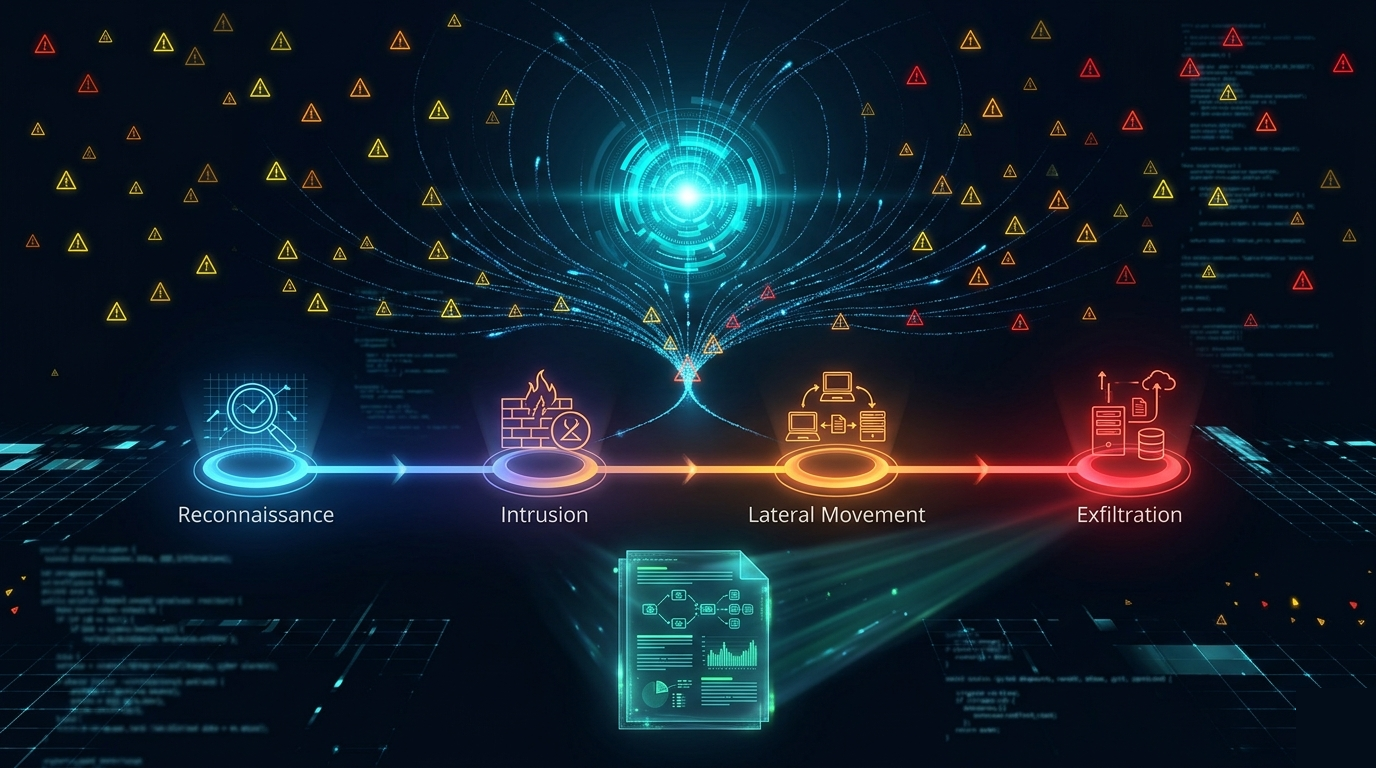
Kill Chain Phase Mapping
Every alert and campaign is mapped to kill chain phases — from initial reconnaissance through lateral movement to exfiltration — so you see exactly where an attack stands.
Indicator Extraction
IPs, usernames, hostnames, domains, and file hashes are automatically extracted and cross-referenced across every alert in the campaign.
Plain-English Narratives
AI generates a human-readable summary of the entire attack campaign — what happened, what's affected, how far it progressed, and what to do next. Ready for executive briefings or incident reports.